What are malicious usb keys and how to create a realistic one?
This blog post shows how to create a reliable and realistic-looking malicious USB key that can be used in a drop attack.

What Is USB Killer Attack and How to Prevent It - IDStrong

The Spies Who Loved You: Infected USB Drives to Steal Secrets
DESCRIPTION Flexible Silicone Replacement Sleeve For Aegis Secure Key 3NX/3NXC and Aegis Secure Key 3z only Not compatible with Aegis Secure Key 3.0

Protective Sleeve Aegis Secure Key 3NX/3Z

What are malicious usb keys and how to create a realistic one?

Beyond the Horizon: Traveling the World on Camaro Dragon's USB

How do I stop old USB drives from infecting my new Windows PC
Why the Security of USB Is Fundamentally Broken
FIPS 140-2 Compliant Design - IP 57 Certified Dust and Water Resistant Unlock with a (7-15 digit PIN) via On-board Keypad Plug-and-Play Software Free

SecureData 8GB SecureUSB KP Encrypted Flash Drive with KeyPad Pin Authentication
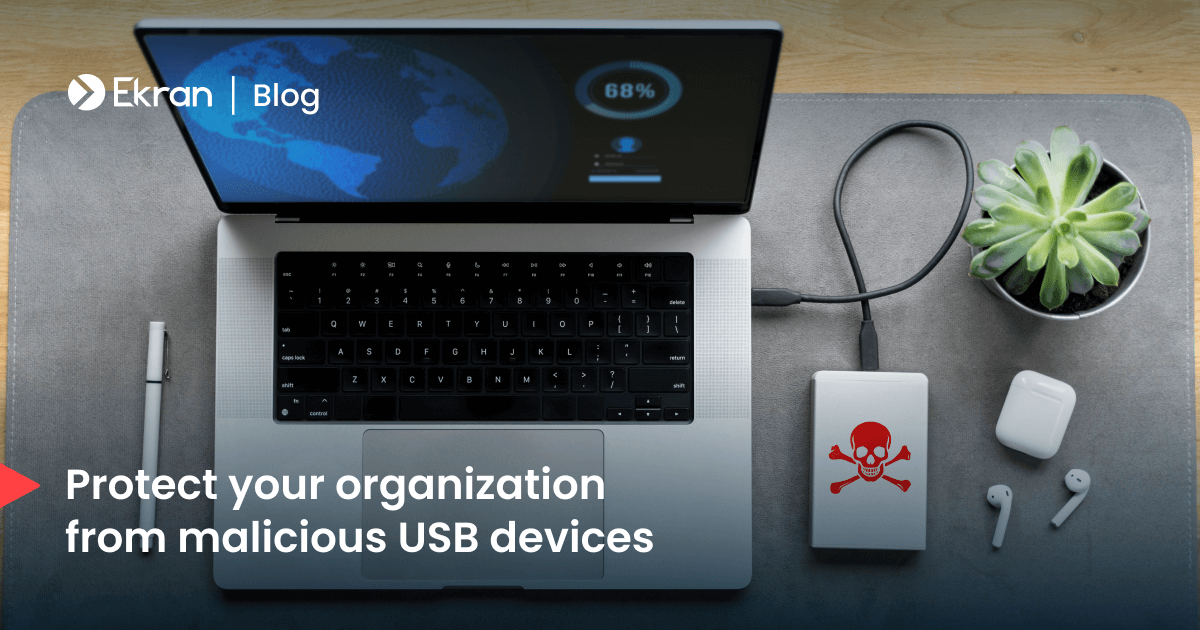
Infected USB Devices: How to Prevent USB-Based Attacks